Recently I needed to get a Cisco ASA 5510 to use a RADIUS Server on Server 2008 to authenticate Active Directory users for VPN access. The ASA was already configured to use a Server 2003 RADIUS server, so much of the below was just replicating the existing configuration on a 2008 server. I suspect many of the settings are less than ideal and some are unnecessary, but the below steps worked for now.
Components
-
AD1:
- Windows Server 2008
- Also the domain controller
- IP: 192.168.1.10
-
CiscoASA:
- ASA 5510 (though I believe these instructions should work for all ASA models)
- IP: 192.168.1.2
Cisco Configuration
I performed the Cisco configuration using the ASDM management tool. The same configuration could be achieved via the command line interface, but I found the ASDM was more convenient for checking existing settings and then replicating.
Launch ASDM and connecting to the ASA, I went to the Configuration view.
Create an IP Name object for the target
- Under the Firewall section, expand the Objects link and select the IP Names.
- Click the Add button at the top.
- Enter a descriptive name, the IP address and a description of the server. For this server I used
- Name: INT-AD1
- IP: 192.168.1.10
- Description: AD / RADIUS
- Click OK and then Apply
Create a new AAA Server Group
- Click the Remote Access VPN section.
- Expand AAA Setup and select AAA Server Groups.
- Click the Add button to the right of the AAA Server Groups section.
- Give the server group a name, like TEST-AD, and make sure the RADIUS protocol is selected.
- Accept the default for the other settings. And click OK
Add the RADIUS server to the Server Group.
- Select the server group created in the step above.
- Click the Add button to the right of Servers in the Select Group.
- Under the Interface Name select the interface on the ASA that will have access to the RADIUS server, most likely inside.
- Under Server Name or IP Address enter the IP Name you created for the RADIUS server above.
- Skip to the Server Secret Key field and create a complex password. Make sure you document this as it is required when configuring the RADIUS server. Re-enter the secret in the Common Password field.
- Leave the rest of the settings at the defaults and click Ok.
Setting Up RADIUS on Windows Server 2008
This part gave me the most trouble. The documentation from Microsoft was somewhat vague and other resources I found using the trusty Google method listed steps and addition pieces I knew to be unnecessary.
To perform the below steps you need Administrator permissions to the server that will host the RADIUS server. You also will need permissions to “Register” the server in AD. I believe this requires Domain Admin privileges.
Add the Network Policy Server function.
- Connect to the Windows Server 2008 server and launch Server Manager.
- Click the Roles object and then click the Add Roles link on the right.
- Click Next on the Before You Begin page.
- Select the Network Policy and Access Services role and click Next.
- Under Role Service select only the Network Policy Server service and click Next.
- Click Install.
After the role finishes installing you will need to set up the server using the Network Policy Server (NPS) management tool found under Administrative Tools.
Registering the server.
- After launching the NPS tool right-click on the entry NPS(Local) and click the Register Server in Active Directory.
- Follow the default prompts.
Create a RADIUS client entry for the ASA.
- Expand the RADIUS Clients and Servers folder.
- Right-click on RADIUS Clients and select New RADIUS Client.
- Create a Friendly Name for the ASA device. I used “CiscoASA” but if you had more than one you might want to make it more unique and identifiable. Make sure you document the Friendly Name used as it will be used later in some of the policies created.
- Enter the Server Secret Key specified on during the ASA configuration in the Shared secret and Confirm shared secret field.
- Leave the default values for the other settings and click OK. See Figure 1 for all the complete RADIUS Client properties.

Figure 1
Create a Connection Request Policy.
- Expand the Policies folder.
- Right-click on the Connection Request Policies and click New.
- Set the Policy Nameto something meaningful. I used CiscoASA because this policy is geared specifically for that RADIUS client. Leave the Type of network access server as Unspecified and click Next.
- Under Conditions click Add. Scroll down and select the Client Friendly Name condition and click Add…
- Specify the friendly name that you used when creating the RADIUS Client above. Click OK and Next.
- On the next two pages leave the default settings and click Next.
- Under the Specify a Realm Name select the Attribute option on the left. From the drop down menu next to Attribute: on the right select User-Name. Click Next again.
- Review the settings on the next page and click Finish.
Create a Network Policy.
- Right-click the Network Policy folder and click New.
- Set the Policy Name to something meaningful. Leave the Type of network access server as Unspecified and click Next.
- Under Conditions click Add.
- Add a UsersGroup condition to limit access to a specific AD user group. You can use a generic group like Domain Users or create a group specifically to restrict access.
- Add a Client Friendly Name condition and again specify the Friendly Name you used for your RADIUS client.
- Click Next. Leave Access granted selected and click Next again.
- (Important Step) On the authentication methods leave the default selection and add Unencrypted authentication (PAP, SPAP).
- Accept the default Constraints and click Next.
- Accept the default Radius Settings and click Next. Review the settings and click Finish.
Restart the Network Policy Server service.
- This may not be necessary, but I did this at various points and cannot be certain the above steps work without restarting the service.
Test Your RADIUS Authentication
The ASDM utility includes functionality to test RADIUS Authentication.
- If necessary re-launch the ASDM utility.
- Return to Configuration -> Remote Access VPN -> AAA Setup -> AAA Server Groups.
- Select the new Server Group you created.
- From the Servers in the Selected Group section highlight the server you created. Click the Test button on the right.
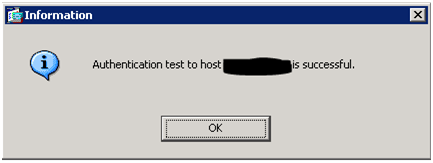
- Select the Authentication radio button. Enter the Username and Password of a user that meets the conditions specified in the Network Policy created above then click OK.
- If everything works as designed you should see something similar to:
Save your Cisco Configuration
Don’t forget to save the running configuration to memory on your ASA. Otherwise you’ll lose all your settings the next time the device is rebooted.
well done! Thanks!
I have tried above settings with an ASA 5510 v8.0(3)12 and Server 2008 R2 but if I try the authentication test in ASDM I keep getting the error message ‘ERROR: Authentication Rejected: AAA failure’.
Is something changed in 2008 R2?
I’m not sure if something changed in R2 or not. And unfortunately I do not have access to an R2 server and an ASA5510 in the same location to test with. If you figure out what has changed please post a comment so I can add it to this post for others to reference. Thanks.
I found the problem, there where 2:
Like Pete Charnock I had problems with the order of the network policy, in my solution I did not disable a policy but I found the right order.
1 ‘Connections to Microsoft routing and Remote Access server’
2 ‘Cisco ASA VPN network’ (this is the policy I created)
3 ‘Connections to other access servers’
Only this order worked (with me)
And second in the network policy the checkbox ‘Ingnore user account dial-in properties’ is by default unchecked, I had to check it to make the policy work.
Excellent guide thank you. I had one more hurdle to overcome which was may RADIUS requests were being dealt with by the wrong network policy.
I tries changing the ordering by putting my policy to the top in the console however the request was still dealt with and rejected by the wrong policy(“Connections to other access servers”).
I disabled the interfering policy and all is now well.
The NPS log is found in c:\windows\system32\logfiles when enabled
Thanks again for good information.
This worked like a champ for me. Thank you!
Worked like a charm. Thanks
Thank you! This worked great for me.
amazing.
It’s not necessary to use unsecured PAP authentication. MS-CHAP and MS-CHAPv2 are also supported authentication protocols, however the process of enabling this is not particularly intuitive.. which is to use password-management command in the VPN tunnel group. This consequently enables password change functionality.. but for those who don’t want to use it, you can disable the password reminder notification by setting the reminder threshold to zero. See http://www.cisco.com/en/US/docs/security/asa/asa82/command/reference/p.html#wp1924502 for details.
Thanks Dan. I’ll have to try that out.
Thanks! This helped me a lot today!
By the way, with the 8.2.x ASA update, you can use ALL forms of Remote Access PPP authentication now. Enable them for your RA profile, and enable them for your NPS server, and the client will negotiate the best case. Or you can just disable the less secure ones like PAP now. PAP is only required to “test” the authentication on the ASA side from what I can tell.
I have opted for the newer EAP methods.
Hi and thanks for your short and ecelent information!
This has saved some hours for search on the web.
bye Arne from Germany (S-H)
This was a great help, I am using server 2008 R2 as well and Dennis’ second help line about the checkbox was what solved my problem.
Thanks worked like a charm.:D
Thanks for this post. Got this up and working in 30 mins. So nice when things just work 🙂
This is a great article and it helped me get an ASA 5505 working with a Windows 2008R2 server. Thanks a bunch. This was much easier than searching through Cisco’s convoluted site!
Thanks, worked great!
Perfect Thanks!!!!!
nice post..i`ll save first n then try
Very useful information. However I keep getting the following error:
***
Authentication test to host XXX failed. Following error occurred –
ERROR: Authentication Rejected: Invalid password
***
I have double checked the key and the Active Directory passwords and the information is correct. Any thoughts of where I need to make the changes to have the configuration work?
Windows 2008 Standard SP2
Cisco ASA 5505 7.2(3) ASDM 5.2
Thank you.
It’s been a long time since I worked with this, but I seem to remember getting a similar error until I changed the authentication protocol. According to a comment from “GoodThings2Life” the 8.2.X ASA update allows you to use all the various protocols.
Thank you for sharing your knowledge.
My test was successful. But I had to disable some network policies.
One of my biggest mistake come from the fact that I was testing the authorization instead of the authentication.
I am to post my screenshoot may be it will help other tech.
Thanks a lot once again.
Great post! Many thanks.
Work Grerat for Win 2008 R2 Server and ASA 8.2(1). Thanks for post!
Thank you VERY much for publishing this article. It worked like a champ. You are correct about Microsoft being vague about Radius/NAP. I will keep this article in my folder!
Please note:
Radius Key must be alphanumeric only
Radius Key must not be too long (it worked with 32 characters, but not with the 66 generated by Windows)
This seems to go against Cisco’s own documentation.
Dude, can i just say you are a genius and awesome. thank you soooooooooo much for this posting. it saved my life and possibly my job! perfect instructions! you are the man!
Mike
You are a gentleman and a scholar.
We lost our 2003 (P)DC before I could finish prepping our new 2008 svr. So after thinking everything was finally back up and running… vpn users started calling. I followed your instructions and within 15 minutes everything worked. Concise, clear, brilliant. You need to start writing tech books.
Many thanks.
Great article !
Helped me immensely in setting up Radius Authentication with 2008 Servers –
Hi, i have setup radius and asa , as per you guided, it’s going fine
i have a problem , in that vpn client , it is remembering last two password. beacuse of this whenever i change the password , the vpn client logging in old password
can help me out
john
Sorry John. I haven’t seen that particular issue. If I understand correctly the VPN is trying to connect using the old password and failing. I would make sure that the VPN client isn’t saving credentials. I don’t have a Cisco VPN client configured that I can look at to see the exact settings available at this time.
You’re a bloody genius mate. I have been searching the net on how to configure the Microsoft RADIUS for days now but couldn’t find a simple to follow step by step guide until I come across your post.
I now have a working Windows Mobile 6.1 VPN (L2TP/IPSec) terminated to an ASA that uses RADIUS server for user authentication.
Thanks again.
Thank you for the detailed instructions. Upgraded from 2003 to 2008 R2 and had to move from NT authentication to RADIUS on our ASA 5520 (as I believe 2008 R2 no longer supports NTLMv1). Also had to follow comments be Dennis (~5 down) to get it to work. All’s working now. Cheers to both of you.
Thank you! Worked great!
This was very helpful. I still had to do a little more in the Cisco ASDM under “Configuration”, Remote Access VPN, “Network (Client) Access, IPsec Connection Profiles, I created a new profile instead of modifying the “authentifation server group” in the existing profile. My SBS2003 is still up and running, I am cutting over in a few days. I am up and able to connect to the old Radius server as well. I just have to change the client setting “group authentication” to match the name of the connection profile from the ASA.
This is absolutely fabulous! Thank you so much. One thing that does need changing though, is the instructions on creating the NAP Connection Request. The last stop, after selecting “User-Name” you have to click Add, leave the fields blank and click OK. Otherwise, the setting of selecting user-name is not saved. This caused me trouble as the tests kept failing.
These instructions work, but not all the the titles are identical for an ASA 5505 with ASDM 5.2.
Again, thank you! You’ve saved me from having to do a lot of research!
Thanks a lot. Truly you are a gentleman and a scholar!!
Has anyone added another step, and got the health policy to work with the RADIUS authentication? I want to also make sure users have firewall on and AV installed before allowing VPN connection.
Great post! I got MS-CHAPv2 working by adding eap-proxy, ms-chap-v2 and enabling password-management per information here: https://supportforums.cisco.com/thread/1004126
Thanks, worked great!
Could I change in my case ASA for router cisco 1841? Is it be working?
I’m sure the process is similar, but I haven’t tested it myself.
your rock!
This worked perfectly on Small Business Server 2011 as well… thank you so much for posting this… i was fine with IAS but NPS is once again M$ way of switching everything around on the Techs just to exercise our brain cells… lol
Great post! I’m soooo close, but I still have an issue:
Any idea why my test authentication works within ASDM, but it will not authenticate when using the client?
Thanks
hehe, oops! I had been using local authentication. I just had to go in and change it to the radius server group created.
Thanks for the great article.
Thank you for the detailed article. I had to make a small change to get my setup to work. I turned on RADIUS server on our domain controller, and I had to choose ‘Windows Groups’ instead of ‘Users Groups’ in step 4 of ‘Create a Network Policy’ section to get it to work.
Worked perfectly thank you very much for your help!!
Great works as documented 🙂
Thank you.
Fantastic information. I was continuously getting hung on one strange error:
“ERROR: Authentication server not responding”
It was then that I realized the domain controller that I have running NPS has two network interfaces.
Once I followed the following procedure the RADIUS test authentication worked like a charm:
To specify the network adapter and UDP ports that NPS uses for RADIUS traffic
Open the NPS console.
Right-click Network Policy Server, and then click Properties.
Click the Ports tab, and prepend the IP address for the network adapter you want to use for RADIUS traffic to the existing port numbers. For example, if you want to use the IP address 192.168.1.2 and RADIUS ports 1812 and 1645 for authentication requests, change the port setting from 1812,1645 to 192.168.1.2:1812,1645.
If your RADIUS authentication and RADIUS accounting UDP ports are different from the default values, change the port settings accordingly.
To use multiple port settings for authentication or accounting requests, separate the port numbers with commas.
Great, Great! I wish all the ‘how to’ info I search for was this easy to follow! I did have to change the Authentication Server Group in my vpn Connection Profile from Local to the AAA RADIUS Server Group I created. If I can get this to work, anyone can. Thank you!
I am getting a mismatched name error in my Server 2008 R2 Network Policy logs in the event viewer. I’ve been troublehsooting it for days with no end or change in status. I followed the tutorial above to a T but am still having an issue. I have a ticket open with MS on it. Most recenently they had me change a registry key to adjust the maxdatagramrequest size…
Has anyone else experienced something similiar?
Many Many thanks!!! It worked for me on first pass!! you have saved me from a bunch of grief…
I had demoted my 2003 DC for a replacement 2008 R2 DC and none of my VPN users (ASA5510) could log in due to authentication (unspecified errors). Once I added the RADIUS server and configured as above all worked a treat.
Thanks again.
Thank you very much.
I had a bit of trouble at first. My cisco 2811 router was trying to authenticate on the same subnet as the Radius, but i had the friendly name (ip) configured on another subnet. Checked the event log, corrected the subnet and it works.
Thanks again
An excellent piece – some minor glitches with the policy order on R2 (as pointed out in one of the comments), but I figured them out before I even read the comments, and now my ASA authenticates against my AD.
One hint for anyone who is trying to do this cross-domain – unless the NPA server is actually IN the domain you’re authenticating against you need to specify fully qualified domain credentials when logging in – eg domain\username, not just username. if the NPA server is running on a DC which is actually IN the domain you want to authenticate against, you can just have the users use their username (no domain specifier necessary).
Probably not an issue for most, but it caught me out as my “infrastructure” servers are not in the same domain of the AD forest as my “user’ servers are – easily worked around, I just enabled the NPA service on one of the “user’ servers so I wouldn’t get the complaints from users like “Why do I have to type in such a long name…”
Cheers and thanks for an excellent article!
Great article. I had to also remove some of my settings in my dynamic access policy in my ASA as I still had LDAP settings in there.
Ohhh my God, ths post wrkd miracles to mi.I wz doomed & the whole world hs collapsed on mi.Straight frm clge, assignd a 802.1x authentication protocol.Never in my life i hd used Ms Server 2008.Tried several postin’ wth no success.Wen i cme acros ths blog my WORLD is light again ‘n’ i feel i’m worthy ths job.Stil tweaking the other parts of the rules coz m using Ms Server 2008 NPS as a radius server to secure wireless infrustructure.
God bles yu.
Mwaaaaah
Thank you for the excellent tutorial. It’s a shame that the ASA cannot browse Windows 2008 R2 or Windows 7 shares.
I just walked a user through setting up their 2008 R2 server as a RADIUS server blindly using this guide. Fantastic documentation!!! Thank you!
Good Job. Helped alot! Thanks!
Hi, thank you very much for the post. I followed your instructions, the test works fine. My question is, do I still need set up Local User on ASA? becuase I use the username and password I’ve set up on server 2008, login fail, is there something I’ve missed?
Any advice will be approciated. Thanks!
You should not need to create local users on the ASA.The exception would be a local administrative user for logging in for administrative purposes if the RADIUS server is offline.
I’d suggest reading through the comments as a number of users have suggested several other steps that helped and changes that have been required due to updates to Server 2008.
Does anyone have any ideas what extra steps are required if you want the ASA to validate users from various different domains?
Never tried it before but it looks like you’ll need to use a RADIUS Proxy server.
Thank you very much for steps given. Really excellent one
Not using Cisco ASA, but a Cisco AP instead (WAP4410N) so I would think it would work on the same principle. Configured the AP and radius server in server 2k8 as described above, but still unable to get it to work. Since the AP doesn’t really have a way to test the connection to the RADIUS, any suggestions as to how to troubleshoot this?
Worked perfectly thank you very much for your help!!
Thanks..
It works but I have a problem. I need the same user to access more then one vpn. Have you ever ever experienced such a problem?
nice article, worked a treat for another router. thx
This worked great for my ASA. Any suggestions on RADIUS with an Aironet 1042?
Great post! Very thorough and concise. Worked perfectly the first time.
Great post. After some testing, i find that it is not actually necessary to create a ‘Connection Reqeust Policy’. in my setup i’ve only created Network Policies, and this works. I’m running Server 2008 R2 btw.
Thank you, great guide.
Saved me a lot of trial and error.
Thanks for your generosity in sharing.
Great guide. Worked like a champ on the first setup attempt. Thanks for saving me a ton of headaches.
Re: Help: ASA 5520 VPN with Radius authentication only using PAP! There are some aaa attributes on the tunnel you can try to adjust:
tunnel-group ppp-attributes
asa(config-ppp)# authentication ?
tunnel-group-ppp mode commands/options:
chap Enable ppp authentication protocol CHAP
eap-proxy Enable ppp authentication to be proxied to an EAP enabled RADIUS
server
ms-chap-v1 Enable ppp authentication protocol MS-CHAP version 1
ms-chap-v2 Enable ppp authentication protocol MS-CHAP version 2
pap Enable ppp authentication protocol PAP
If setting the above doesn’t work, try to enable password-management which will require the ASA to send mschap-v2 plus you get the added benefit of the feature which is explained here:
http://www.cisco.com/en/US/docs/security/asa/asa80/command/reference/p.html#wp1879916
I have the problem : Eventid 6273, Authentication failed due to a user credentials mismatch ; Reason code: 16; Do you have an idea?
Not sure. Sounds like you might have the username or password wrong. Or maybe the domain is off.
I’m sure of my password, I have verified several times 🙂
Either the user name provided does not map to an existing user account.
Configuration on Cisco 1921
I have configured the Cisco from CLI
I have tested with W8, MacOs, iOs, Android all is perfect but with W7 unable to connect. Do you have an idea?
The problem is solved; bad password between cisco and radius!
Thanks a lot 🙂
Great guide!
I have tested with W8, MacOs, iOs, Android all is perfect but with W7 unable to connect. Do you have an idea?
Its 18:11 on June 14 ’13 and this page ahs just saved me 10 hours work and a few hundred Quid.
thanks a million mate it does EXACTLY what it says on the bloody tin. 🙂
Nice write up it saved me TONS of time since I am a Cisco guy and not a Microsoft one. Only problem i had was it didn’t like the common password it wanted me to use the Server shared secret in the Radius setup for the ASA.
awesome guide …..first time …easy radius config
awesome guide
thanks
Awesome! I am running Windows 2012 R2 and ASA5520 Version 9.1(2) and your guide worked like a charm!!
Many Thanks!
You are awesome. I was working on this project from 15 days without any success but you made my day. Thanks a lot.
Thanks, worked a treat except… the cisco devices have locally set user limit to 15. Now I get access rejected when there are 5 users connected to the local device. If i clear a session from the cosco device i can access again. There are not connection limits set in AD so a little stumped.
So, I get to the step to Add a UsersGroup condition to limit access to a specific AD user group. What is the problem if that User Group does not appear in the list? I do not have those, or the Computers groups. I checked to see if the RADIUS server is registered in AD, and it is, so I’m a bit lost..
It’s been a long time since I’ve had to set this up. If it doesn’t list the groups can you try to add them manually. You’d just need to make sure the name matches. Worth a shot.
Ok, I’ve got a stupid question I guess, but I don’t really use Cisco for anything but site-to-site VPNs, but what VPN client can you use? I am trying this, and the test from the ASDM to my RADIUS server is successful, but I am not able to connect to the ASA using a Windows VPN. I’ve played with the security settings in the client but still nothing. Do I have to use the Cisco client to get this to work? Thanks!
With Cisco you have to use a compatible VPN client which to my knowledge does not include the Windows VPN. Cisco has their AnyConnect client but you have to have a valid log in to their site and a license that entitles you to it. I’ve also had luck with Shrew Soft’s VPN client.
Just a note on Test from the ASDM under the AAA Server Group/Servers in the Selected Group – it only tests with PAP. So if you are like us and use the password management to enable only MS-CHAPv2 (And the Obscurity Award goes to Cisco…) then you can only test from a real AnyConnect VPN client and not ASDM. HIPAA requires only encrypted authentication and connection when using a VPN, so keep this in mind if HIPAA is a constraint for you. And who wants clear text PAP stuff running around anyway.
Great guide, Save me a great deal of time, I was missing the “(Important Step)”!
Keep it up.
Hi, I am using EVE-NG and have followed the steps to setup Radius on Cisco Switch, but I am still getting Event ID6273 and Reason Code 49. I am not sure if anyone has tried these steps on Cisco Switch and Aruba Controller with Aruba Campus AP. I have not been able to get any of these devices working. Hope someone can help